What is Vulnerability Management and Scanning?
As company systems have become more complex, opportunities for vulnerability have also increased. Companies leverage cloud technologies, 3rd party vendors, and hybrid systems to fuel their operations. Unfortunately, this infrastructure creates more access points that hackers can use as attack surfaces.
This is why having a comprehensive vulnerability management program can help secure your system from threats.
“Vulnerability management involves applications, people, and systems that can mitigate risk in a good time”.
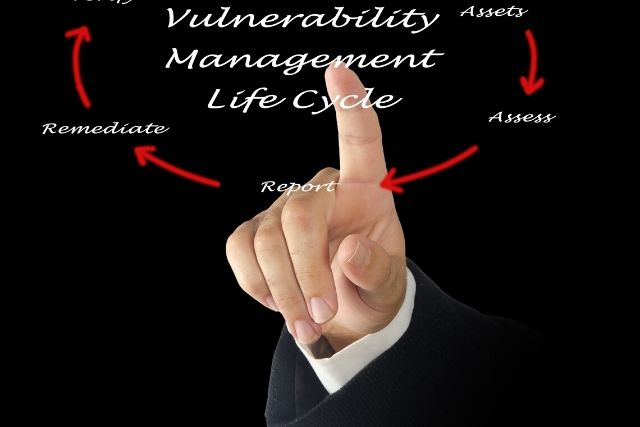
But how does it work? The essential components of a vulnerability management program include identifying and managing potential attacks before they can cause damage to your business.
This may be done via intelligent automated systems that use past data as a reference point, or by an active team that regularly analyzes your network for potential threats. Understanding vulnerability management is critical because your business can implement systems that detect and repel malicious activity.
Defining Vulnerability Management
By definition, “Vulnerability Management is the process of identifying, classifying, and mitigating security weaknesses in your systems“. It is an on-going process that includes many different elements- from resource allocation to timely reporting.
Any company that’s operating in today’s world will need to practice vulnerability management to complement its risk management. Because such workflows have become a requirement for audit, risk, and compliance programs, your business should be capable of assessing and taking action on relevant information.
The best way of determining weaknesses in your systems is by being proactive. This means constantly analyzing incoming data, organizing information into relevant categories, and determining how various threats could affect your corporate systems.
Technology has made it much easier to implement vulnerability management programs. For example, automated scanners can be used to collect, analyze, and understand threats across the entire system.
Artificial intelligence is also useful for analyzing previous data so that you can uncover patterns of vulnerability across your infrastructure. These insights provide the necessary information that can be applied to vulnerability management programs.
More specifically, machine learning is a useful tool where data can be analyzed to uncover threats, weak spots, and opportunities for mitigation.
Implementation Of Vulnerability Management In Your Business
Effective vulnerability management systems should work continuously to detect, analyze, and mitigate threats within your infrastructure. But how can you develop such a system and operate it within your current framework? It starts with:
1. Identifying Threats to Company Systems
The primary purpose of vulnerability management is identifying which threats your systems face and how such threats can be controlled. This is why identifying all vulnerabilities is critical.
By using automated scanning systems, you can continuously analyze incoming data from multiple sources to identify potential risks. Furthermore, such data can be compared to previous records to expedite the analysis process.
2. Evaluation of Threats/Vulnerabilities
Data collection and threat identification is only the first step towards vulnerability management. Once data has been collected, it needs to be analyzed to determine the specific risks that may affect your systems.
You can also use a vulnerability management framework to assign risk ratings and categorize threats appropriately. For example, the Common Vulnerability Scoring System (CVSS) provides a useful framework for evaluating threats and prioritizing them appropriately.
You can use it to maintain a proactive approach towards keeping your systems secure against hackers.
3. Responding to Vulnerabilities Within Current Systems
After identifying and evaluating threats, the next step is to develop an elaborate response plan. Specific responses will vary depending on the type of vulnerability being dealt with.
More specifically, your response to vulnerability should be based on the nature of your business, network, and shareholders.
Vulnerability response can be carried out in 3 different ways. First, remediation is typically used to fix weaknesses within your systems fully, so they aren’t exploited at a future date.
If the vulnerability can’t be fully remediated, another useful response is mitigation. Mitigation is a method of reducing the damage that risk might cause.
It should be implemented as a temporary step, allowing more time for the organization to develop a remediation plan for the vulnerability in question.
The third available option is vulnerability acceptance. If the risk is low enough such that it doesn’t affect essential operations, you may choose to accept the risk as part of your operating environment.
This means being aware of the vulnerability but not taking any action towards remediation.
4. Reporting
Continuous improvement is a critical part of vulnerability management. The best way of continuously improving your ability to detect threats is by generating reports from previous activity.
Such reports form an archive that represents the nature of your risk environment. They also provide actionable insights that you can use to improve the speed and accuracy through which vulnerabilities can be detected.
Reporting is an asset that your IT workers can use to streamline threat identification, analysis, and remediation. By implementing more effective techniques of data surveillance, teams can collaborate in real-time and continue to improve their vulnerability profiles.